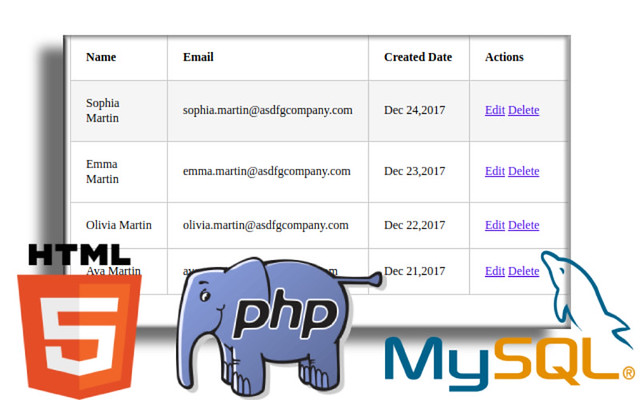
In this post, I aim to shed light on the insidious threat known as SQL injection and, more importantly, how to fortify your website against such attacks. SQL injection is a common and potentially devastating vulnerability that can leave your website exposed to malicious intent. It’s essential to understand its workings and take measures to prevent it from compromising your web application’s data and security.
In today’s digital landscape, security is paramount for any PHP website. SQL injection attacks remain a persistent threat, capable of compromising sensitive data and undermining user trust. This article serves as your guide to fortifying your PHP website against SQL injection. We’ll explore effective methods, best practices, and robust security measures that will help you safeguard your web application and maintain the integrity of your data.
SQL Injection:
SQL injection is another vulnerability of PHP. SQL injection refers to the act of anyone can inserting a MySQL statement to be run on our database without our knowledge. Injection usually occurs when you ask a user for input, like their name, and instead of a name they give you a MySQL statement that you will unknowingly run on your database.
Example :
MYSQL Query :
$username = ‘Anil’;
It will run successfully.
If we use a bad username like : $username=”OR 1”
Normal Query :
Injected Query :
Here quote() is treated as end of that query , its like
username = ”
after that add OR 1
OR 1 means it is always true, so that we can get all information without knowing of username also, same problem with delete query also.
To prevent these injections always use mysql_real_escape_string() or addslashes().
if (get_magic_quotes_gpc()) {
$name = stripslashes($name);
}
$name = mysql_real_escape_string($name);
select * from users where username= ‘$name’;
Now we can prevent the website from SQL Injection.
In conclusion, safeguarding your PHP website from SQL injection is not just a recommendation; it’s a necessity in the ever-evolving world of cybersecurity. As web applications become more sophisticated, so do the tactics employed by malicious actors. However, by implementing the security measures detailed in this article, you’re taking a significant step towards preserving the privacy and trust of your users.
Remember, a secure PHP website is the cornerstone of a successful online presence. By staying proactive in your approach to security and consistently monitoring for vulnerabilities, you can build a robust defense against SQL injection and other threats. Embrace these best practices, and empower your PHP website to thrive in an environment where security is paramount.





10 Comments
PHPGangsta · April 12, 2010 at 8:20 pm
Perhaps it’s also a good tip to use prepared statements, that prevents SQL Injection, too.
Michiel Bakker · April 12, 2010 at 9:24 pm
Great to see you’re checking for “get_magic_quotes_gpc()”. I sometimes tend to forget that while it can be quite important.
Don’t forget that SQL injection doesn’t just cover MySQL, it’s something that can occur on usage of any database server.
Nayan Paul · April 24, 2010 at 1:54 pm
I think these is best for Prevent SQL Injection
function makeEncode($sql)
{
$sql = preg_replace(sql_regcase(“/(from|select|insert|delete|where|drop table|like|show tables|\’|’\| |=|-|;|,|\|’||#|\*|–|\\\\)/”), “” ,$sql);
$sql = trim($sql);
$sql = strip_tags($sql);
$sql = (get_magic_quotes_gpc()) ? stripslashes($sql) : mysql_real_escape_string($sql);
$sql = htmlentities($sql);
return $sql;
}
Tim Zappa · January 31, 2011 at 10:50 pm
>SQL injection is another vulnerability of PHP.
As polite as I can possibly say it… You are an idiot! PHP/SQL works exactly as it should. It is the incompetent and inexperienced programmers that create these security holes.
Charlie B · February 4, 2011 at 6:12 pm
This isn’t only a PHP issue, or a particular database issue, but every language and every database is vulnerable, as well as other storage technologies like XML/XPath.
Magic quotes and strip slashes can help mitigate the risk, but using parametrized queries will stop every way of injecting. I would re-write the code to:
$query= “select * from users where username=?”; //query definition
$preparedStatement=$database_connection()->prepare($query); //prepare the statement
mysqli_stmt_bind_param($preparedStatement, ‘s’, $field1); //prepare to bind a Strings (the s)
$field1 = $name; //you may want to do more input checking here!
mysqli_stmt_execute($preparedStatement); //execute the parametrized query
I have a very in depth article on the same
https://www.golemtechnologies.com/articles/prevent-sql-injection-attacks
phphunger · June 5, 2012 at 12:19 pm
As per my knowledge every programming language faces such kind of attacks..but the major thing is as php is a loosly typed language..so the attacking is some what severe…but as the new versions are keep on releasing all the flaws are being overcome in the lastest versions..As i have written something about SQL Injections in my blog also with some extra information..can find here..http://phphunger.blogspot.in/2012/06/how-to-prevent-php-code-from-sql.html
Rahul · March 8, 2015 at 10:13 am
Great information about SQL injection
Test Now: Is Your Web Site Or Web Application Vulnerable To SQL Injection Attacks? | Aafrin.com · October 23, 2010 at 3:12 am
[…] How To Prevent PHP Website From SQL Injection […]
Είναι το web site σας ασφαλές σε SQL Injection επιθέσεις; « Web Resources · November 4, 2010 at 4:51 am
[…] How To Prevent PHP Website From SQL Injection […]
SQL Injection: How To Prevent Security Flaws In PHP / MySQL · November 9, 2010 at 7:09 pm
[…] http://www.anil2u.info/2010/04/12/how-to-prevent-php-website-from-sql-injection/ […]